Scan Monthly No. 009November 2003 |
 |
<< Other Issues of Scan Monthly |
Signals of Change
China's Global Designs
SoC033
Not satisfied with making gradual progress up the value chain, China has opened initiatives to compete in global markets on a wide variety of fronts simultaneously. In addition to making rapid progress in scientific and technical R&D, computer programming, and electrical engineering, China is breaking into the world of product design. Western companies are even beginning to turn to Chinese creatives to design advertising campaigns.
eScience
SoC034
The bad news is that information technology (IT) allows scientists to generate unmanageable amounts of experimental data. The good news is that IT provides scientists with new tools to analyze and share the data and collaborate in ways they never have before. Scientists' race to develop the capabilities to handle the data is creating a fortuitous spiral of increasing productivity. Computation- and network-intensive scientific techniques are creating practices and procedures that make up the new domain that many people call eScience.
Brand Exhaustion
SoC035
In a world of intense competition for consumer attention, some brands, ironically, are running into problems with overexposure—just think Jennifer Lopez and Ben Affleck. Multichannel ad campaigns, cobranded products, multiproduct franchises, and impossible-to-control buzz and word-of-mouth marketing all create increased risks of overexposing or exhausting a brand. The traditional strategy of grabbing as much attention as possible is, for most brands, obsolete: Consumers' attention is sufficiently valuable now that consumers will resent anyone who abuses it.
The United States of Asia
SoC036
Those of us who dwell on the impossibility of an Asian union comparable to the European Union or the United States will miss out on the fact that a union of economic expediency is emerging among some Asian countries. Japan is already China's largest export market, and South Korea's exports to China now exceed its exports to the United States. Three industry associations in China, Japan, and South Korea recently agreed to sponsor an organization to facilitate the development of open-source software solutions as a means of combating an overdependence on Microsoft products. Because it's informal and undeclared, this Asian union stands a good chance of taking some Western companies by surprise.
Insights
| Health-Care Applications of Pervasive-Computing Technologies | View summary |
| D03-2450 | |
|
With some parts of the worldwide health-care industry about to go on life support because of high costs and demand for newly available services, health-care organizations are keen to cut costs and pursue efficiencies. Pervasive-computing technologies hold great potential for helping to achieve these goals. Pervasive-computing health-care applications fall roughly into two categories: technologies that enhance the handling of data, information, and knowledge and technologies that play an integral role in medical diagnosis and treatment processes. This study describes academic and corporate efforts to design and implement pervasive-computing health-care environments. Most efforts combine existing technologies, such as sensors, radio-frequency identification tags, wireless local-area networks, and handheld-computing devices to create interactive, context-aware environments. Although some people believe that the market for pervasive computing in a health-care setting is poised for dramatic rapid growth, developers have yet to address completely the issues of wireless data-transmission interference, security, battery life, data overload, privacy, and physician resistance to change. Author: Greg Powell. 7 pages. Index Keywords: Aging Population; Biotechnology; Computer Networks; Health Care; Information Technology; Research and Development; Sensors. |
|
| Strategies for Privacy-Related Business Issues | View summary |
| D03-2451 | |
|
This study highlights approximately 40 of the most interesting data points that the Scan process has identified in the past several months in the area of privacy. The study deals with the data points in five categories that constitute an integrated privacy strategy for any business. The first category deals with the establishment of a coherent and consistent internal privacy policy by the organization. The second involves transparent implementation of planned privacy-threatening technologies: Customers and employees need to know exactly what the organization will and will not use particular technologies for. The third category has to do with the creation of provisions for an organization's own privacy—or its security. The fourth category involves the hard bargain that customers are increasingly striking in any exchange of information— customers are demanding real and tangible benefits in exchange for private information. The fifth category deals with the pros and cons of allowing customers to opt out of revealing private information whenever possible. Author: Martin Schwirn. 12 pages. Index Keywords: Business Ethics; Consumer Behavior; Information Technology; Security Industry; Social Trends. |
|
| Business Perspectives on Emergence | View summary |
| D03-2452 | |
|
Emergence is the term that researchers use to describe the appearance of sophisticated or complex behavior patterns from the confluence of uncoordinated actions of large numbers of independent agents. Emergence is attracting interest in the business community in several ways. First, companies are using a growing understanding of emergence to characterize better complex systems that they encounter in the business environment in which they must function and grow. An understanding of emergence provides them with new perspectives on everything from the global economy to an individual consumer's purchase-decision process and from how buzz marketing rips through a population to the dynamics of the company's own organizational structure. Second, researchers are currently experimenting with applying the concepts of emergence for entertainment and business applications. Will Wright's Sim City game is an example in the entertainment arena, and Southwest Airline's freight-routing system is an example in the business arena. Third, emergence is a prominent trait of complex adaptive systems in the natural world, so companies are interested in studying which characteristics of emergence might help organizations become more adaptive to the turbulent commercial environment. The traditional command-and-control organizational structures and planning processes have their limits, and the complex adaptive systems of nature may shed light on alternatives. Author: Kermit M. Patton. 7 pages. Index Keywords: Computer Software; Consumer Behavior. |
|
| Prospects for Ultrawideband Communications | View summary |
| D03-2453 | |
|
During recent years, spread-spectrum technologies enabled companies to increase wireless data rates, reduce power consumption, and control interference by spreading the energy of radiated emissions over a wide range of frequencies. Taking this principle to the next step, ultrawideband (UWB) technologies can spread energy out over a range of frequencies even wider than that of spread-spectrum techniques, promising to increase the usable data rate of wireless technology dramatically while minimizing interference with conventional sources. UWB is a revolutionary technology and thus faces many challenges in becoming accepted by regulators, suppliers, and end users. Only start-up companies such as XtremeSpectrum are wagering their business strategy on the success of UWB. Larger companies such as Intel, Motorola, and Texas Instruments are maintaining active development efforts but do not rely on UWB's becoming part of their core business—in contrast to the existing 802.11 variants, which are indeed now part of core business for those companies. This study, developed with SRI Consulting Business Intelligence's Digital Futures program, examines applications, industry developments, and business-development issues for this promising but controversial technology. Author: Michael Gold. 6 pages. Index Keywords: Communications; Computer Networks, Consumer Electronics; Information Technology; Telecommunications. |
|
Calendar
Scan™ Briefings
The 2003 biannual Scan™ Briefings in which Scan staff present Scan analysis and findings in Menlo Park, California, will take place on:
- 20 May 2004 at 8:00 am
- 21 October 2004 at 8:00 am
Scan™ Abstract Meetings
Scan abstract meetings (in which SRIC-BI [now SBI] staff participate in a free-form discussion of current Scan abstracts) are open for client observation/participation on:
- 21 January 2004 at 9:00 am
- 17 March 2004 at 9:00 am
- 19 May 2004 at 1:30 pm
- 21 July 2004 at 9:00 am
- 22 September 2004 at 9:00 am
- 20 October 2004 at 1:30 pm
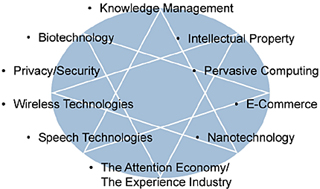
Watch List
The Scan program's scanning and research processes identify areas on the periphery of your organizations's focus that constitute potential opportunities or threats. The areas that we decide bear watching go on Scan's watch list of defining forces that are transforming the business environment. Current watch-list topics include: